Archivefhdjuq986mp4 Link Apr 2026
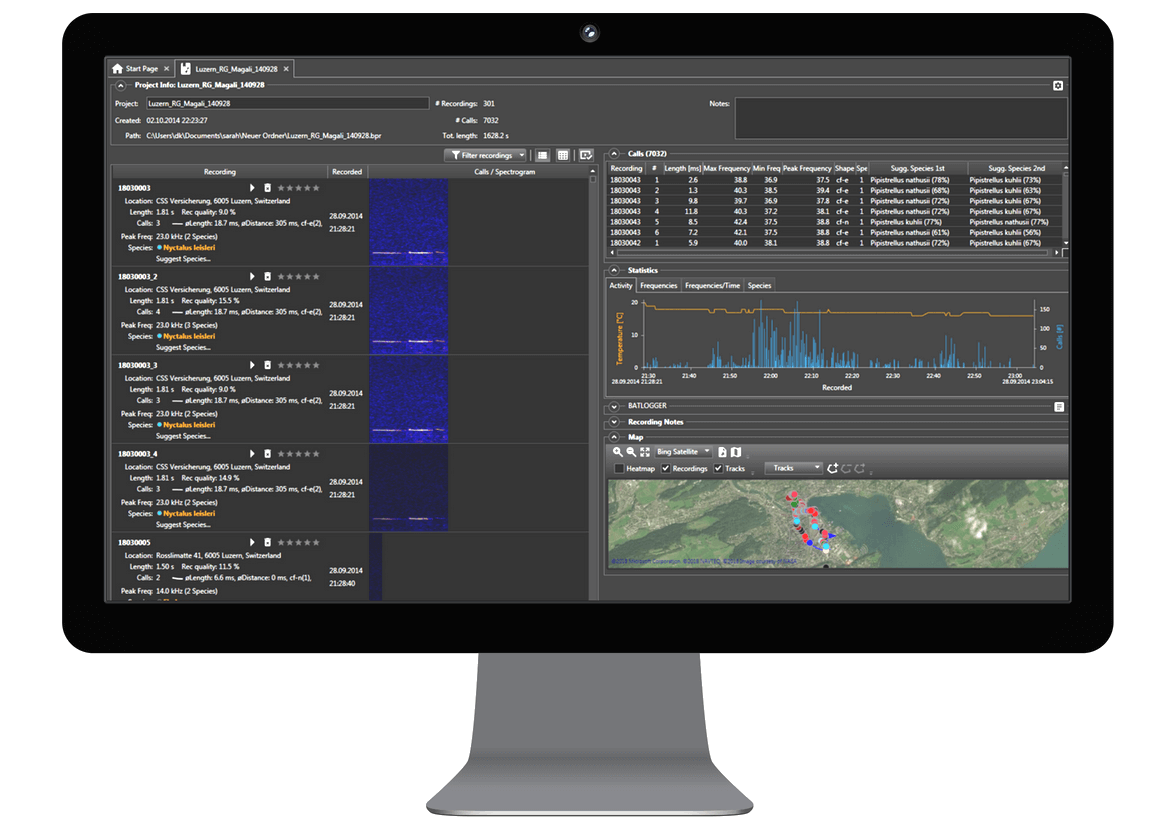
Analyse your recordings
Organize recordings easily and fast
Automatic bat call detection
Listening, viewing and classifying recordings
Automate recurring actions with tasks
Bat species suggestions
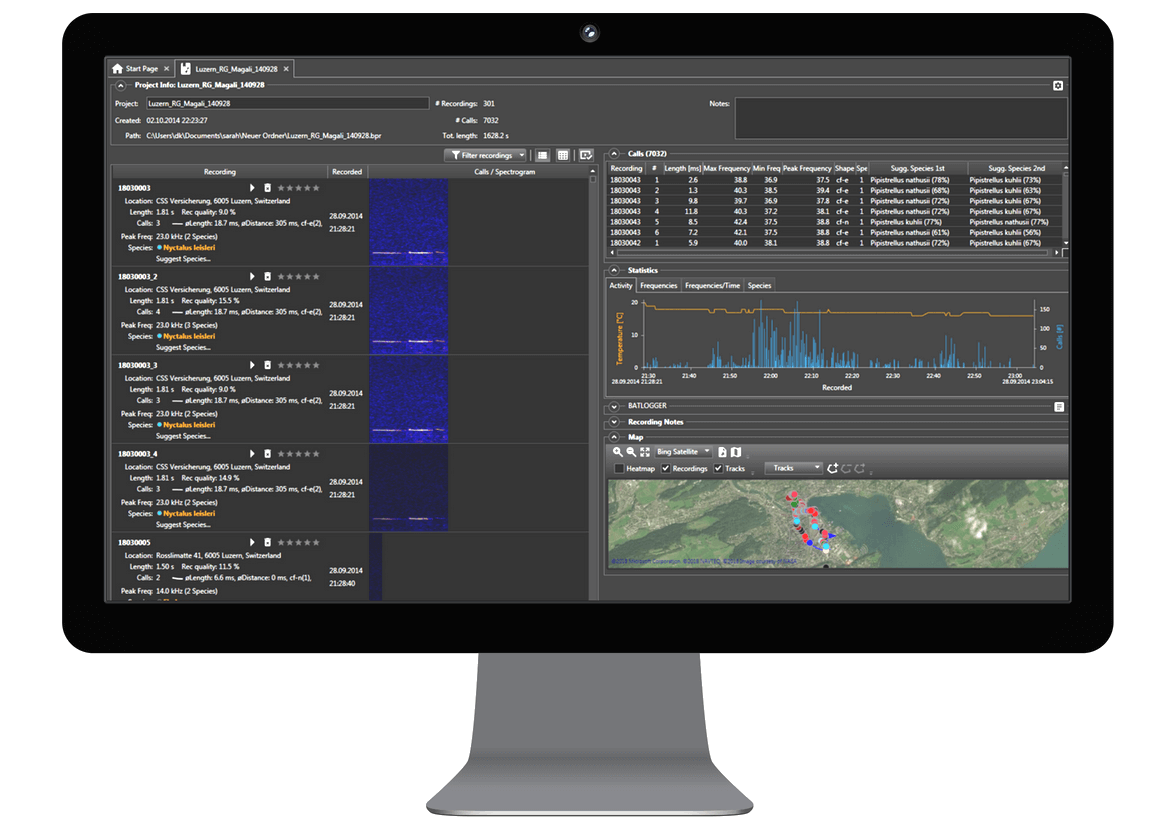
Organize recordings easily and fast
Automatic bat call detection
Listening, viewing and classifying recordings
Automate recurring actions with tasks
Bat species suggestions
Finally, the string points to the economics and infrastructure of digital preservation. Maintaining archives—ensuring storage redundancy, format migration (to avoid bit rot), and long-term governance—requires resources. When content is reduced to an opaque filename, it can obscure the labor and cost behind preservation efforts. Advocates for open, well-funded archives argue that transparent identifiers and accessible metadata help justify investment and enable reuse by educators, researchers, and the public.
The social dimension matters too. Shared links—especially terse ones—circulate through communities differently than polished metadata-rich entries. In informal networks, a short link can function as an in-group token: those who recognize the pattern or source will follow it; outsiders will ignore or distrust it. This dynamic shapes how media spreads, who gains access, and how cultural artifacts are preserved or lost. In scholarly contexts, however, persistent, well-documented links underpin citation and reuse; a scholarly archive’s credibility depends on clear identifiers and stable access.
Access and rights management are equally implicated. The presence of an “archive” in a filename does not guarantee open access; archives balance preservation with legal and ethical constraints. Copyright, privacy concerns, and cultural sensitivities can determine whether a file is publicly linkable or restricted. Platforms sometimes generate opaque links specifically to limit casual discovery, enabling controlled sharing without embedding content in search indexes. Thus, the cryptic link may reflect intentional access design as much as technical happenstance. archivefhdjuq986mp4 link
In sum, the concise, cryptic label “archivefhdjuq986mp4 link” is more than a random filename: it encapsulates tensions central to contemporary digital culture—between machine efficiency and human meaning, privacy and access, anonymity and trust, ephemeral sharing and long-term preservation. How we name, identify, and expose digital objects shapes not only their technical retrievability but their cultural afterlife. Clear metadata, robust provenance, thoughtful access controls, and sustainable infrastructure transform opaque tokens into reliable artifacts of the digital record—ensuring that what we archive today remains discoverable, usable, and meaningful tomorrow.
This leads to questions about discoverability and metadata. A cryptic token is efficient for machines but impoverished for human readers. Without descriptive metadata—title, creator, date, subject, or rights information—the object risks becoming a “digital orphan”: preserved technically but effectively inaccessible because people cannot assess its relevance or provenance. Archivists and digital librarians therefore emphasize rich, structured metadata and persistent identifiers (like DOIs or ARKs) to link opaque storage keys to meaningful contextual information. The tension between machine-generated identifiers and human-readable descriptions reflects the broader challenge of making large-scale digital archives usable. Finally, the string points to the economics and
The phrase "archivefhdjuq986mp4 link" reads like a compact, technical marker—an alphanumeric token appended to a filename or URL that implies a specific digital object: an MP4 video file stored or shared via an archive. Though on its face the string is nonsensical, it opens a window onto broader themes about digital preservation, metadata practices, access, and the social life of media in the internet age.
First, consider what such a filename signals. Filenames that embed seemingly random character sequences—“fhdjuq986,” for example—often arise from automated systems: content delivery networks, cloud storage services, or web platforms that assign unique identifiers to prevent collisions and to route requests. The “mp4” extension identifies a container format ubiquitous for video, and the leading term “archive” suggests intentional preservation rather than ephemeral posting. Together, these elements evoke a workflow in which content is ingested, processed, and stored by systems that privilege scalability and retrievability over human-friendly naming. In informal networks, a short link can function
Another theme is trust and authenticity. A link labeled only by a hash-like string can raise doubt: Who uploaded this file? Is it legitimate? Has it been altered? In response, modern archival practice layers integrity checks (cryptographic hashes), provenance records, and version control to assure users of authenticity. Public archives often publish policies and provenance trails so researchers and the public can evaluate the chain of custody. Absent such signals, anonymous links invite suspicion—especially in an era when deepfakes and manipulated media complicate visual evidence.
More information about the software can be found in the Online User Guide.