Final Dev Letter & FAQ
2025-01-29
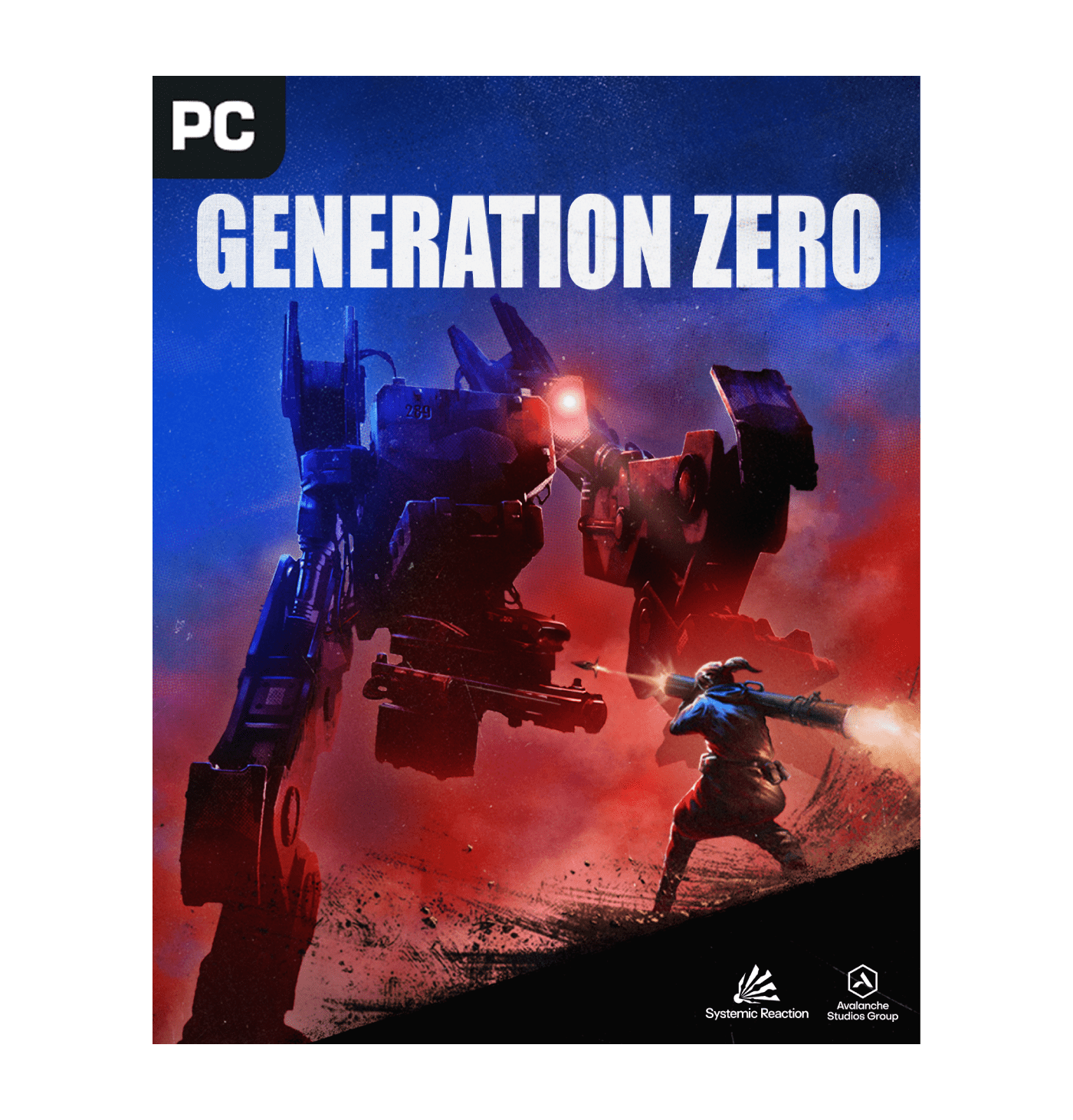
Explore a vast open world, rendered with the award-winning Apex engine, featuring a full day/night cycle with unpredictable weather, complex AI behavior, simulated ballistics, highly realistic acoustics, and a dynamic 1980’s soundtrack.
Experience an explosive game of cat and mouse set in a huge open world. In this reimagining of 1980’s Sweden, hostile machines have invaded the serene countryside, and you need to fight back while unravelling the mystery of what is really going on. By utilizing battle tested guerilla tactics, you’ll be able to lure, cripple, or destroy enemies in intense, creative sandbox skirmishes.
Go it alone, or team-up with up to three of your friends in seamless co-op multiplayer. Collaborate and combine your unique skills to take down enemies, support downed friends by reviving them, and share the loot after an enemy is defeated.
All enemies are persistently simulated in the world, and roam the landscape with intent and purpose. When you manage to destroy a specific enemy component, be it armor, weapons or sensory equipment, the damage is permanent. Enemies will bear those scars until you face them again, whether that is minutes, hours, or weeks later.
Key Features could include secure boot, runtime integrity, tamper detection, and secure key storage. Each feature needs a brief explanation. For example, secure boot prevents unauthorized code execution by verifying the digital signature of firmware.
The user mentioned the "21" in the title. Maybe that's a version number, like Trust Architecture Version 21. I should clarify if there are previous versions and what updates or improvements V21 includes. However, since I don't have access to specific NXP documentation, I'll have to make educated guesses based on general knowledge.
In Technical Details, I can delve into components like the Trusted Execution Environment (TEE), TrustZone technology, and cryptographic modules. I should discuss how these components work together to provide a security layer. Maybe mention specific cryptographic algorithms used, like AES, RSA, SHA, and the role of hardware security modules (HSMs).
The Introduction should set the context, explaining the importance of secure boot, secure communication, and hardware-based security in modern computing. Then, an overview of Qoriq Trust Architecture (QTA-21) would be necessary. I should mention that it's designed for NXP's Qoriq processors, which are used in industrial, automotive, and networking applications.
I need to ensure that the paper is accessible but still technical, avoiding too much jargon while explaining concepts clearly. Also, since the user provided the title, I should make sure the paper aligns with a User Guide, but since it's a draft, it's more of an explanation and reference guide.
Potential challenges in writing this paper include the lack of specific details about QTA-21 since it's a hypothetical or less-documented topic. However, using general knowledge about secure architectures and NXP's offerings can help fill in the gaps.
Understanding the Qoriq Trust Architecture 21: A Comprehensive User Guide
I should also mention compliance with standards like Common Criteria or ISO standards, if applicable. Security certifications might be important here.
Read the latest news from the Generation Zero development team.